Customer Experience (CX): Definition, Importance, and Strategies for Success
Tue, 25 February 2025

Follow the stories of academics and their research expeditions

About Ethical Hacking Tools and Software
Penetration testing, also known as ethical hacking, has changed dramatically since advanced automatic tools became accessible. By optimizing the testing procedure, these techniques help enterprises in protecting their data and infrastructural facilities. Partnering with penetration testing service providers further enhances this process by ensuring expert-led vulnerability assessments and comprehensive security evaluations. To improve the abilities of security experts and strengthen defences against hacking attacks, an organization's security strategy must include cyberattacks. Cybersecurity boot camps and courses offer essential training to help these efforts.
As technology gets better, cyberthreats become more challenging and widespread. To ensure data in a particular security of personal and organizational digital era, ethical hacking tools are important. Professionals in cybersecurity can use these tools to find weak points, model possible attacks, and build strong defenses. New developments in ethical hacking tools have gotten better in their practicality in 2026. Those very same days, ethical hacking techniques are great for stopping breaches and securing adherence to digital security laws, no matter how small or big a corporation is.
Here are the Top Ethical Hacking Tools for 2026 includes:
1) Invicti
Description: Invicti is a powerful web application security scanner that automates the detection of vulnerabilities like SQL Injection and XSS. With its unique Proof-Based Scanning Technology, it delivers accurate results with minimal configuration.
Features:
Scans up to 1,000 web applications within 24 hours.
Detects custom URL rewrite rules and 404 error pages.
Integrates seamlessly with SDLC and bug tracking systems via REST API.
2) Fortify WebInspect
Description: This comprehensive tool offers dynamic analysis for complex web applications, enabling security professionals to identify vulnerabilities by testing the behavior of running applications.
Features:
Centralized program management with vulnerability trending.
Risk oversight with simultaneous crawling for varied testing levels.
Provides in-depth statistics and relevant information for effective scanning.
3) Cain & Abel
Description: A versatile password recovery tool, Cain & Abel is primarily used for recovering Microsoft Access passwords and sniffing network traffic.
Features:
Supports dictionary, brute-force, and cryptanalysis attacks.
Uncovers encrypted passwords effectively.
Free and open-source, making it accessible for all users.
4) Nmap (Network Mapper)
Description: Nmap is a command-line tool that is well-known because of its port scanning capabilities. It can identify hosts and services on a network extensive network and produce an map.
Features:
Supports advanced vulnerability detection.
Adapts to network conditions during scans.
Offers a graphical interface for easier usability.
5) Nessus
Description: Nessus is an essential tool for network safety since it is a top vulnerability scanner that can identify serious errors and configurations in a system.
Features:
Identifies unpatched services and weak passwords.
Detects various system vulnerabilities efficiently.
Free for non-enterprise use.
6) Nikto
Description: Nikto is indeed an open-source web scanner that verifies web servers for security flaws such as risky CGIs and out-of-date software.
Features:
Checks for over 6,400 vulnerabilities.
Performs version-specific checks across multiple servers.
Identifies misconfigured files and insecure programs.
7) Kismet
Description: Kismet as it is a an outstanding tool for testing wireless communications network detector as well as snort that inactively gathers packets reveals hidden networks, and helps analyze wireless caller activity.
Features:
Works with various wireless cards in raw-monitoring mode.
Capable of detecting non-beaconing networks.
8) NetStumbler
Description: A Windows-based tool that helps detect wireless networks and prevents wardriving, NetStumbler is essential for network configuration and troubleshooting.
Features:
Identifies access point configurations.
Assesses signal strength and interference.
Detects unauthorized access points.
9) Acunetix
Description: Fully automated, Acunetix scans for over 4,500 web vulnerabilities, supporting JavaScript, HTML5, and single-page applications.
Features:
Offers a consolidated view of scanning results.
Integrates with various platforms for enhanced risk prioritization.
Provides comprehensive reporting for risk management.
10) Netsparker
Description: A tool that mimics hacker behavior, Netsparker identifies vulnerabilities in web APIs and applications with precision.
Features:
Verifies identified vulnerabilities to eliminate false positives.
Available as both an online service and Windows software.
Streamlines the verification process, saving valuable time.
11) Intruder
Description: Intruder is a vulnerability scanner that detects security flaws in cybersecurity and helps in their efficacious remedial work.
Features:
Over 9,000 security checks are carried out.
Quickly combines with Jira and Slack, among other tools.
Prioritizes vulnerabilities based on context for efficient management.
12) Metasploit
Description: A powerful framework for penetration testing, Metasploit enables ethical hackers to create and run exploit codes against distant targets.
Features:
Cross-platform compatibility across different OSs.
Ideal for identifying security vulnerabilities.
Facilitates the creation of anti-forensic tools.
13) Aircrack-Ng
Description: As wireless usage rises, Aircrack-Ng offers command-line tools for assessing Wi-Fi security and performing testing activities.
Features:
Offers support for a variety of operating systems, including Windows and Linux.
WPA2-PSK and WEP keys can be cracked.
Allows for data exportation to text files.
14) Wireshark
Description: Wireshark excels in analyzing data packets, providing deep inspections of a wide range of protocols.
Features:
Supports live captures and offline analysis.
Cross-platform compatibility.
Offers color-coded packet lists for easy identification.
15) OpenVAS
Description: OpenVAS is a comprehensive vulnerability assessment tool designed for large-scale scans, performing both authenticated and unauthenticated testing.
Features:
Supports various Internet and industrial protocols.
Backed by a robust programming language for customization.
16) SQLMap
Description: SQLMap is an open-source tool that makes this possible to manage database servers by instantly identifying potential SQL Injection vulnerabilities.
Features:
Supports multiple SQL injection techniques.
Provides a powerful detection engine for vulnerabilities.
Compatible with various database systems, including MySQL and PostgreSQL.
17) Ettercap
Description: A versatile tool best known for its capabilities in network and host analysis, Ettercap allows for the creation of custom plug-ins.
Features:
Content filtering and live connection sniffing.
Active and passive dissection of various protocols.
Supports a wide range of network configurations.
18) Maltego
Description: Maltego is an effective link analysis tool that is especially well-suited for big datasets and is used for data analysis and actual data collection.
Features:
Provides graphical representations of data relationships.
Enhances different operating systems like Windows and Linux.
Makes efficient data analysis with user-friendly visuals.
19) Burp Suite
Description: Burp Suite, besides being a well-known security testing tool, occurs in many price tiers, free community edition. It provides vulnerability scanning.
Features:
Supports scan scheduling and repeating.
Integrates with continuous integration (CI) systems.
Provides comprehensive reporting and analytics.
20) John the Ripper
Description: This popular password cracking tool is designed to detect weak UNIX passwords and supports multiple operating systems.
Features:
Customizable cracker with various attack modes.
Performs dictionary attacks for efficient password recovery.
Tests a wide range of encrypted passwords.
21) Social-Engineer Toolkit (SET)
Description: SET is a powerful tool focused on social engineering attacks, allowing testers to create phishing sites and conduct various social engineering techniques.
Features:
Supports multi-platform deployment.
A user-friendly interface makes it simple to use.
Enables phishing templates to be highly customized.
22) ZAP (Zed Attack Proxy)
Description: ZAP is an open-source web application security detector that is meant for both developers and hackers.
Features:
Provides automated scanners and various tools for manual testing.
User-friendly GUI with comprehensive documentation.
Actively maintained with regular updates.
23) Cyborg Hawk Linux
Description: Cyborg Hawk Linux is a vulnerability-scanning and penetration testing Linux distribution that offers a variety of tools for experts.
Features:
User experience-focused design and an easy installation process.
Supports various hacking tools for security testing.
Customizable desktop environment.
24) BackBox
Description: Another specialized Linux distribution for penetration testing and security assessments, BackBox provides an extensive repository of open-source tools.
Features:
Lightweight and efficient with a focus on usability.
Integrated support for security analysis and auditing tools.
Regular updates to ensure up-to-date security measures.
25) Parrot Security OS
Parrot Security OS is a security-focused operating system comprised of various security tools, designed for cybersecurity professionals and security professionals.
Features:
Easy-to-use interface for navigation.
Extensive support for a variety of security testing instruments.
Offers a secure environment for testing and analysis.
26) YARA
Description: Research teams can efficiently identify and describe recognition and characterization. threats thanks to YARA, a potent tool for spyware
Features:
Supports complex rule writing for efficient malware detection.
Integrates with other security tools for enhanced functionality.
User-friendly syntax for ease of use.
27) Pangur
Description: Pangur is a network monitoring and analysis tool that provides insights into network behavior and performance.
Features:
Supports real-time monitoring of network traffic.
Offers detailed reporting and analytics.
User-friendly interface for efficient navigation.
28) Commix
Description: Commix automates the process of testing for command injection vulnerabilities in web applications, enabling penetration testers to identify weaknesses effectively.
Features:
Offers various injection techniques for comprehensive testing.
Provides a user-friendly command-line interface.
Regular updates to support new vulnerabilities.
29) Fuzzbunch
Description: Fuzzbunch is a framework developed by the NSA for exploiting vulnerabilities, enabling security professionals to test their systems comprehensively.
Features:
Supports various payloads for testing vulnerabilities.
Provides an extensive library of exploits.
User-friendly interface for streamlined operations.
30) Burp Collaborator
Description: Burp Collaborator is an essential penetration testing tool that makes it easier to test web applications for security flaws and out-of-band interactions.
Features:
Supports various interaction types for testing.
Integrates seamlessly with Burp Suite.
Provides detailed reporting and analytics.
31) Sifter
Description: Sifter is an open-source penetration testing tool that assists in testing web applications for vulnerabilities, enabling security professionals to identify weaknesses efficiently.
Features:
Supports a wide range of testing techniques.
User-friendly interface for easy navigation.
Regular updates to support new vulnerabilities.
32) Puppet
Description: Puppet is an automation platform for configuration management which helps businesses deploy but rather manage software uniformly throughout their infrastructure.
Features:
Provides version control for configuration files.
Supports a wide range of operating systems.
User-friendly interface for easy navigation.
33) Tenable.io
Description: Tenable.io is a cloud-based vulnerability tool that enables up-to-date information on security flaws across a facility.
Features:
Supports continuous monitoring and analysis.
Provides detailed reporting and analytics.
Integrates seamlessly with other security tools.
34) Kali Linux
Description: Kali Linux, a popular Linux distribution designed for penetration testing, is a favourite among security experts since it comes pre-installed with a wide range of hacking tools.
Features:
Offers a customizable desktop environment.
Supports a wide range of tools for various testing scenarios.
Regularly updated to ensure up-to-date security measures.
35) Cyborg Hawk
Description: Cyborg Hawk is an advanced Linux distribution built specially for ethical hacking. It has an easy user interface and a variety of security tools for penetration testing.
Features:
Supports various ethical hacking tools for security testing.
Easy installation process for new users.
Regular updates to keep tools current and effective.
As new software and tools are created to bolster defenses against cyberattacks, ethical hacking is always changing. Regardless of experience level, adding these 35 tools to one's toolbox can significantly improve the ability to protect processes. Keeping abreast of the most recent ethical hacking techniques and trends is essential to creating a thorough security plan. Sprintzeal recognize how critical it is to this industry. Our IT training courses are aimed at supporting to professionals stay up to date with the latest trends in cybersecurity, learn ethical hacking tools, and improve their situations.
Penetration testing, also known as ethical hacking, has changed dramatically since advanced automatic tools became accessible. By optimizing the testing procedure, these techniques help enterprises in protecting their data and infrastructural facilities. Partnering with penetration testing service providers further enhances this process by ensuring expert-led vulnerability assessments and comprehensive security evaluations. To improve the abilities of security experts and strengthen defences against hacking attacks, an organization's security strategy must include cyberattacks. Cybersecurity boot camps and courses offer essential training to help these efforts.
As technology gets better, cyberthreats become more challenging and widespread. To ensure data in a particular security of personal and organizational digital era, ethical hacking tools are important. Professionals in cybersecurity can use these tools to find weak points, model possible attacks, and build strong defenses. New developments in ethical hacking tools have gotten better in their practicality in 2026. Those very same days, ethical hacking techniques are great for stopping breaches and securing adherence to digital security laws, no matter how small or big a corporation is.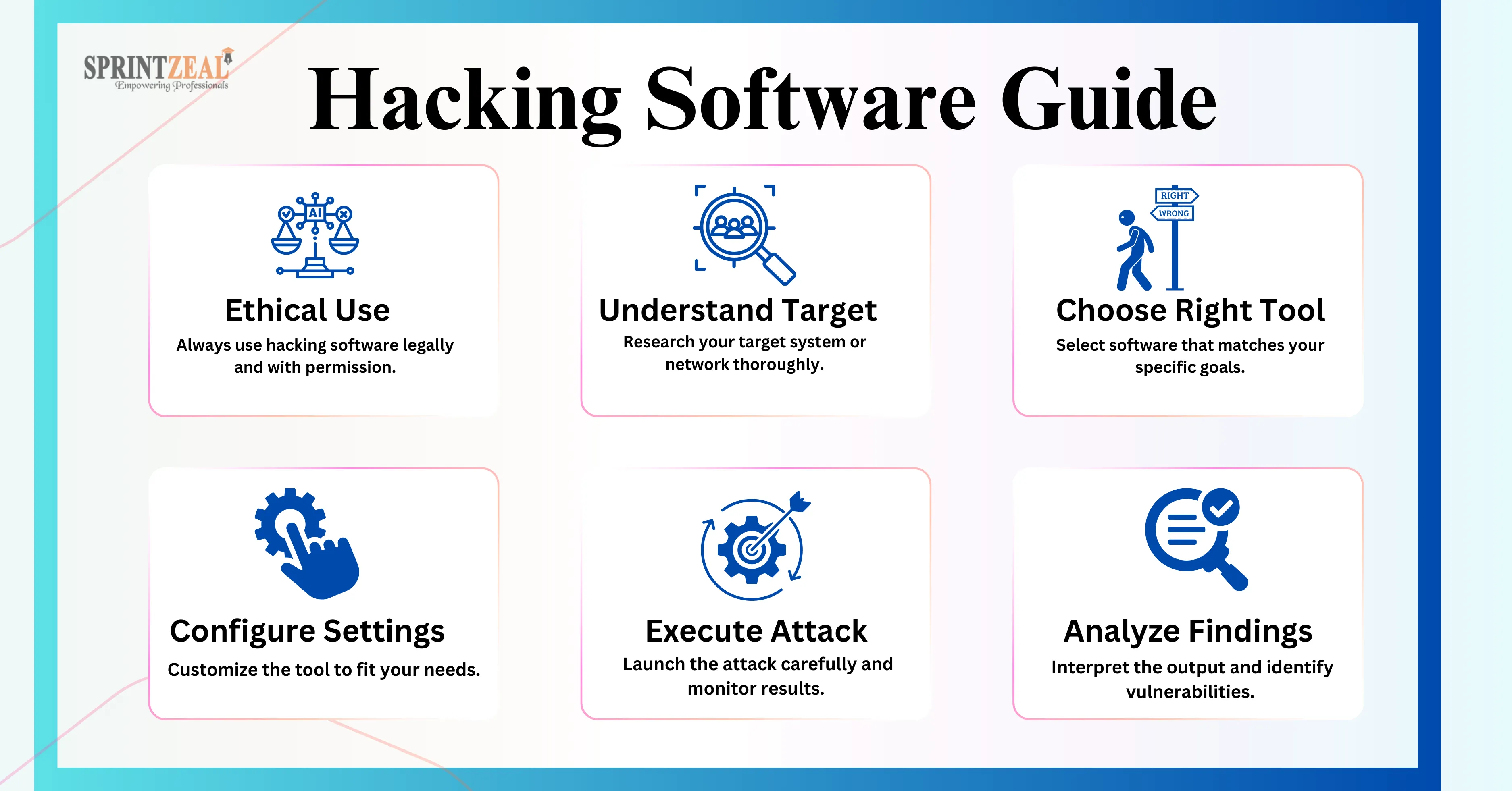
Here are the Top Ethical Hacking Tools for 2026 includes:
1) Invicti
Description: Invicti is a powerful web application security scanner that automates the detection of vulnerabilities like SQL Injection and XSS. With its unique Proof-Based Scanning Technology, it delivers accurate results with minimal configuration.
Features:
Scans up to 1,000 web applications within 24 hours.
Detects custom URL rewrite rules and 404 error pages.
Integrates seamlessly with SDLC and bug tracking systems via REST API.
2) Fortify WebInspect
Description: This comprehensive tool offers dynamic analysis for complex web applications, enabling security professionals to identify vulnerabilities by testing the behavior of running applications.
Features:
Centralized program management with vulnerability trending.
Risk oversight with simultaneous crawling for varied testing levels.
Provides in-depth statistics and relevant information for effective scanning.
3) Cain & Abel
Description: A versatile password recovery tool, Cain & Abel is primarily used for recovering Microsoft Access passwords and sniffing network traffic.
Features:
Supports dictionary, brute-force, and cryptanalysis attacks.
Uncovers encrypted passwords effectively.
Free and open-source, making it accessible for all users.
4) Nmap (Network Mapper)
Description: Nmap is a command-line tool that is well-known because of its port scanning capabilities. It can identify hosts and services on a network extensive network and produce an map.
Features:
Supports advanced vulnerability detection.
Adapts to network conditions during scans.
Offers a graphical interface for easier usability.
5) Nessus
Description: Nessus is an essential tool for network safety since it is a top vulnerability scanner that can identify serious errors and configurations in a system.
Features:
Identifies unpatched services and weak passwords.
Detects various system vulnerabilities efficiently.
Free for non-enterprise use.
6) Nikto
Description: Nikto is indeed an open-source web scanner that verifies web servers for security flaws such as risky CGIs and out-of-date software.
Features:
Checks for over 6,400 vulnerabilities.
Performs version-specific checks across multiple servers.
Identifies misconfigured files and insecure programs.
7) Kismet
Description: Kismet as it is a an outstanding tool for testing wireless communications network detector as well as snort that inactively gathers packets reveals hidden networks, and helps analyze wireless caller activity.
Features:
Works with various wireless cards in raw-monitoring mode.
Capable of detecting non-beaconing networks.
8) NetStumbler
Description: A Windows-based tool that helps detect wireless networks and prevents wardriving, NetStumbler is essential for network configuration and troubleshooting.
Features:
Identifies access point configurations.
Assesses signal strength and interference.
Detects unauthorized access points.
9) Acunetix
Description: Fully automated, Acunetix scans for over 4,500 web vulnerabilities, supporting JavaScript, HTML5, and single-page applications.
Features:
Offers a consolidated view of scanning results.
Integrates with various platforms for enhanced risk prioritization.
Provides comprehensive reporting for risk management.
10) Netsparker
Description: A tool that mimics hacker behavior, Netsparker identifies vulnerabilities in web APIs and applications with precision.
Features:
Verifies identified vulnerabilities to eliminate false positives.
Available as both an online service and Windows software.
Streamlines the verification process, saving valuable time.
11) Intruder
Description: Intruder is a vulnerability scanner that detects security flaws in cybersecurity and helps in their efficacious remedial work.
Features:
Over 9,000 security checks are carried out.
Quickly combines with Jira and Slack, among other tools.
Prioritizes vulnerabilities based on context for efficient management.
12) Metasploit
Description: A powerful framework for penetration testing, Metasploit enables ethical hackers to create and run exploit codes against distant targets.
Features:
Cross-platform compatibility across different OSs.
Ideal for identifying security vulnerabilities.
Facilitates the creation of anti-forensic tools.
13) Aircrack-Ng
Description: As wireless usage rises, Aircrack-Ng offers command-line tools for assessing Wi-Fi security and performing testing activities.
Features:
Offers support for a variety of operating systems, including Windows and Linux.
WPA2-PSK and WEP keys can be cracked.
Allows for data exportation to text files.
14) Wireshark
Description: Wireshark excels in analyzing data packets, providing deep inspections of a wide range of protocols.
Features:
Supports live captures and offline analysis.
Cross-platform compatibility.
Offers color-coded packet lists for easy identification.
15) OpenVAS
Description: OpenVAS is a comprehensive vulnerability assessment tool designed for large-scale scans, performing both authenticated and unauthenticated testing.
Features:
Supports various Internet and industrial protocols.
Backed by a robust programming language for customization.
16) SQLMap
Description: SQLMap is an open-source tool that makes this possible to manage database servers by instantly identifying potential SQL Injection vulnerabilities.
Features:
Supports multiple SQL injection techniques.
Provides a powerful detection engine for vulnerabilities.
Compatible with various database systems, including MySQL and PostgreSQL.
17) Ettercap
Description: A versatile tool best known for its capabilities in network and host analysis, Ettercap allows for the creation of custom plug-ins.
Features:
Content filtering and live connection sniffing.
Active and passive dissection of various protocols.
Supports a wide range of network configurations.
18) Maltego
Description: Maltego is an effective link analysis tool that is especially well-suited for big datasets and is used for data analysis and actual data collection.
Features:
Provides graphical representations of data relationships.
Enhances different operating systems like Windows and Linux.
Makes efficient data analysis with user-friendly visuals.
19) Burp Suite
Description: Burp Suite, besides being a well-known security testing tool, occurs in many price tiers, free community edition. It provides vulnerability scanning.
Features:
Supports scan scheduling and repeating.
Integrates with continuous integration (CI) systems.
Provides comprehensive reporting and analytics.
20) John the Ripper
Description: This popular password cracking tool is designed to detect weak UNIX passwords and supports multiple operating systems.
Features:
Customizable cracker with various attack modes.
Performs dictionary attacks for efficient password recovery.
Tests a wide range of encrypted passwords.
21) Social-Engineer Toolkit (SET)
Description: SET is a powerful tool focused on social engineering attacks, allowing testers to create phishing sites and conduct various social engineering techniques.
Features:
Supports multi-platform deployment.
A user-friendly interface makes it simple to use.
Enables phishing templates to be highly customized.
22) ZAP (Zed Attack Proxy)
Description: ZAP is an open-source web application security detector that is meant for both developers and hackers.
Features:
Provides automated scanners and various tools for manual testing.
User-friendly GUI with comprehensive documentation.
Actively maintained with regular updates.
23) Cyborg Hawk Linux
Description: Cyborg Hawk Linux is a vulnerability-scanning and penetration testing Linux distribution that offers a variety of tools for experts.
Features:
User experience-focused design and an easy installation process.
Supports various hacking tools for security testing.
Customizable desktop environment.
24) BackBox
Description: Another specialized Linux distribution for penetration testing and security assessments, BackBox provides an extensive repository of open-source tools.
Features:
Lightweight and efficient with a focus on usability.
Integrated support for security analysis and auditing tools.
Regular updates to ensure up-to-date security measures.
25) Parrot Security OS
Parrot Security OS is a security-focused operating system comprised of various security tools, designed for cybersecurity professionals and security professionals.
Features:
Easy-to-use interface for navigation.
Extensive support for a variety of security testing instruments.
Offers a secure environment for testing and analysis.
26) YARA
Description: Research teams can efficiently identify and describe recognition and characterization. threats thanks to YARA, a potent tool for spyware
Features:
Supports complex rule writing for efficient malware detection.
Integrates with other security tools for enhanced functionality.
User-friendly syntax for ease of use.
27) Pangur
Description: Pangur is a network monitoring and analysis tool that provides insights into network behavior and performance.
Features:
Supports real-time monitoring of network traffic.
Offers detailed reporting and analytics.
User-friendly interface for efficient navigation.
28) Commix
Description: Commix automates the process of testing for command injection vulnerabilities in web applications, enabling penetration testers to identify weaknesses effectively.
Features:
Offers various injection techniques for comprehensive testing.
Provides a user-friendly command-line interface.
Regular updates to support new vulnerabilities.
29) Fuzzbunch
Description: Fuzzbunch is a framework developed by the NSA for exploiting vulnerabilities, enabling security professionals to test their systems comprehensively.
Features:
Supports various payloads for testing vulnerabilities.
Provides an extensive library of exploits.
User-friendly interface for streamlined operations.
30) Burp Collaborator
Description: Burp Collaborator is an essential penetration testing tool that makes it easier to test web applications for security flaws and out-of-band interactions.
Features:
Supports various interaction types for testing.
Integrates seamlessly with Burp Suite.
Provides detailed reporting and analytics.
31) Sifter
Description: Sifter is an open-source penetration testing tool that assists in testing web applications for vulnerabilities, enabling security professionals to identify weaknesses efficiently.
Features:
Supports a wide range of testing techniques.
User-friendly interface for easy navigation.
Regular updates to support new vulnerabilities.
32) Puppet
Description: Puppet is an automation platform for configuration management which helps businesses deploy but rather manage software uniformly throughout their infrastructure.
Features:
Provides version control for configuration files.
Supports a wide range of operating systems.
User-friendly interface for easy navigation.
33) Tenable.io
Description: Tenable.io is a cloud-based vulnerability tool that enables up-to-date information on security flaws across a facility.
Features:
Supports continuous monitoring and analysis.
Provides detailed reporting and analytics.
Integrates seamlessly with other security tools.
34) Kali Linux
Description: Kali Linux, a popular Linux distribution designed for penetration testing, is a favourite among security experts since it comes pre-installed with a wide range of hacking tools.
Features:
Offers a customizable desktop environment.
Supports a wide range of tools for various testing scenarios.
Regularly updated to ensure up-to-date security measures.
35) Cyborg Hawk
Description: Cyborg Hawk is an advanced Linux distribution built specially for ethical hacking. It has an easy user interface and a variety of security tools for penetration testing.
Features:
Supports various ethical hacking tools for security testing.
Easy installation process for new users.
Regular updates to keep tools current and effective.
As new software and tools are created to bolster defenses against cyberattacks, ethical hacking is always changing. Regardless of experience level, adding these 35 tools to one's toolbox can significantly improve the ability to protect processes. Keeping abreast of the most recent ethical hacking techniques and trends is essential to creating a thorough security plan. Sprintzeal recognize how critical it is to this industry. Our IT training courses are aimed at supporting to professionals stay up to date with the latest trends in cybersecurity, learn ethical hacking tools, and improve their situations.
Tue, 25 February 2025

Mon, 31 March 2025

Tue, 25 February 2025


© 2024 Sprintzeal Americas Inc. - All Rights Reserved.
Leave a comment